Go back
Inside Nexus
Product
March 20, 2026

Highlights
Helix introduces a hybrid architecture where IoT data remains in traditional databases while its integrity is anchored on-chain through cryptographic hashes, ensuring verifiability without sacrificing scalability or cost efficiency.
This proof-of-concept demonstrates how organizations can independently verify sensor data authenticity, eliminate reliance on trusted intermediaries, and build tamper-evident audit trails for compliance and operational decision-making.
By combining blockchain-based integrity with AI-driven validation, Helix enables real-world use cases such as logistics tracking, healthcare monitoring, and automated workflows built on provable, trustworthy data.
From Data Storage to Data Verifiability
Data is only as valuable as the trust you can place in it.
In industries like logistics, compliance, healthcare, and industrial monitoring, a single manipulated datapoint can invalidate audits, disrupt operations, or cause financial disputes. As AI systems increasingly depend on data, the issue of verifiability of data becomes more pressing.
At Nuklai, we've built an IoT proof-of-concept on our Helix blockchain that demonstrates a simple but powerful principle: Store operational data in a traditional database, but anchor its authenticity on-chain.
How Hash Anchoring Secures IoT Data
Traditional databases are efficient and flexible, but they are not tamper-proof. Administrators can modify records, malicious actors can gain access, and historical integrity is hard to prove without complex audit systems.
Our approach adds a cryptographic verification layer:
Sensor data is stored in a backend database for operational use
The same data + timestamp is hashed
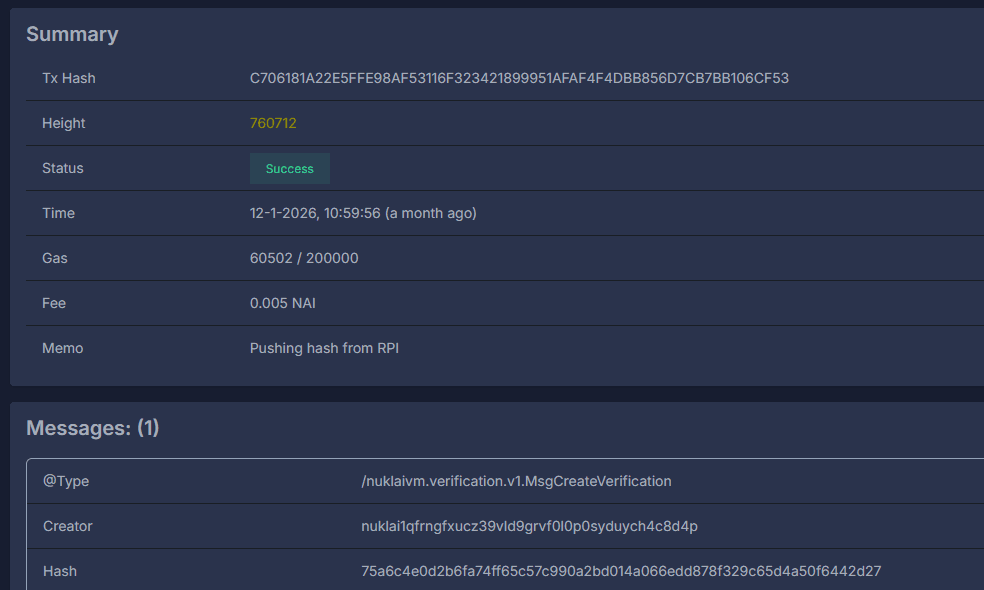
The hash is stored immutably on the Helix blockchain
At any later time, the database record can be re-hashed
If the hash matches the blockchain entry: the data is authentic
Because blockchain records cannot be changed retroactively, the chain acts as a permanent cryptographic fingerprint of reality at a given moment in time.
We are not storing raw data on-chain, only hashes. This preserves scalability, privacy, and efficiency while still guaranteeing integrity. But just as important: it remains cost-efficient. Similar offerings exist, yet many effectively become expensive data solutions, while the IoT market is highly competitive and cost-driven with the necessity to scale on billions of transactions and records.
Proof-of-Concept Architecture in Practice
To validate the approach end-to-end, we implemented a production-style IoT traceability PoC that mirrors common industrial architectures.
The setup:
An edge device/gateway (representative of deployed IoT hardware)
A connected temperature sensor (industrial/field sensor equivalent)
A backend data store for complete time-series logs
Helix for immutable integrity anchoring via hashes (fingerprints)
On a one-minute interval, the edge component collects a measurement, enriches it with a timestamp and device metadata, stores the full entry off-ledger, computes a hash of the stored record, and writes only that hash to Helix.
This process runs continuously and creates a parallel audit trail that cannot be modified.
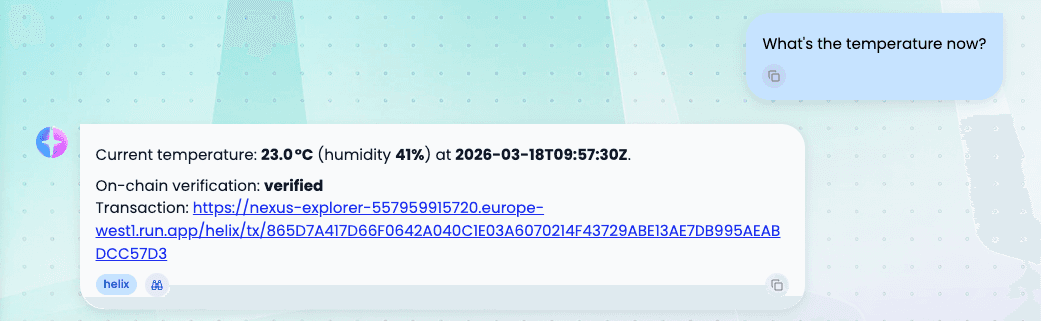
Later, anyone with access can independently verify the results by retrieving the temperature record from the database, hashing it again, and comparing it against the anchored integrity record.
Matching hashes prove authenticity. Any mismatch reveals tampering. No trust in the database operator is required because verification is purely mathematical.
On top of this, an AI-driven decision process can automatically validate incoming data against the integrity proofs and make downstream decisions (e.g., flag anomalies, trigger alerts, block actions, or approve workflows) based only on verified, untampered sensor records.
Real-World Impact: From Disputes to Proof
Imagine a logistics company transporting temperature-sensitive goods.
A shipment arrives spoiled. The supplier claims the truck failed to maintain proper cooling. The logistics company insists their system worked correctly. Without verifiable data, this becomes a dispute based on trust. With blockchain-anchored sensor data the recorded temperatures can be verified and cannot be rewritten.
The same principle applies to:
Pharmaceutical cold chain monitoring
Food safety tracking
Industrial sensor logs
Compliance reporting
Smart infrastructure telemetry
AI training data provenance
Anywhere data authenticity matters, blockchain anchoring provides cryptographic proof.
Building Data Lineage by Default
Beyond simple verification, this architecture enables full data lineage.
Every datapoint receives a timestamp, a cryptographic fingerprint and an immutable reference, creating an audit trail that answers critical questions:
When was this data created?
Has it ever changed?
Can we independently prove its origin?
For organizations operating under regulatory pressure, this becomes a built-in compliance layer rather than an afterthought.
A key design principle of this use case is that blockchain is not replacing databases. Instead, it acts as a “trust anchor”. Databases remain fast and flexible. Blockchain guarantees integrity.
This hybrid architecture avoids the scalability limitations of on-chain storage while still delivering cryptographic certainty. It is a practical path toward enterprise-grade blockchain adoption without forcing organizations to rebuild their infrastructure.
Helix Testnet Is Live in Nexus
Helix is now available as a data source inside Nexus, currently running in testnet.
This is more than a proof-of-concept. It is a live environment where verifiable data workflows can already be explored, tested, and built on.
This signals two important things. First, development on Helix is active and progressing toward production readiness. Second, Helix is already being integrated into real product surfaces, not developed in isolation.
From a utility perspective, this is where $NAI becomes tangible.
Every integrity event on Helix, from anchoring a datapoint to verifying a transformation, is designed to be powered by $NAI. As these workflows move from testnet to mainnet and from experiments to enterprise use cases, $NAI becomes the operational layer behind data trust, traceability, and verification.
Inside Nexus, this integration brings that utility closer to users. Instead of thinking about blockchain as a separate system, it becomes part of how data is queried, validated, and acted on.
See For Yourself
This proof-of-concept is live in Nexus. In order to play around with it to get a better understanding of it:
Go to Configuration > AI > Agents
Select an existing agent or create a new one based on an existing LLM model configuration
Click the gear icon on that agent to configure tools
Choose “Internal Tools” and then Helix
Add the available Helix tools
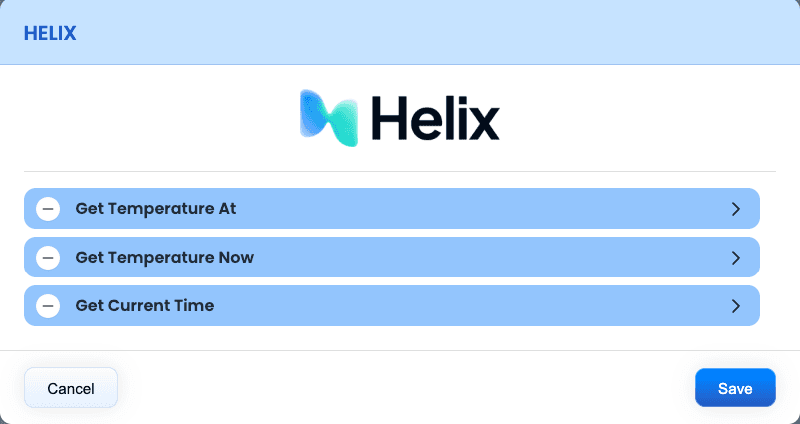
You can then proceed to the chat interface, start a new chat with your configured agent and start asking it questions about the temperature data.
Establishing Trust as a Data Layer
This proof-of-concept shows how data integrity can move from assumption to certainty.
As AI systems increasingly rely on real-world data, the ability to verify that data becomes foundational. Helix provides that trust layer, without changing how organizations store or operate on their data.
If your workflows depend on data being correct, consistent, and provable, this is where that future starts.
👉 Explore it directly in Nexus: https://nexus.nukl.ai







